Troubleshooting ethernet
Table Of Contents
Full-Duplex Operation 10/100/1000
Troubleshooting Ethernet
Ethernet was developed by Xerox Corporation's Palo Alto Research Center (PARC) in the 1970s. Ethernet was the technological basis for the IEEE 802.3 specification, which was initially released in 1980. Shortly thereafter, Digital Equipment Corporation, Intel Corporation, and Xerox Corporation jointly developed and released an Ethernet specification (Version 2.0) that is substantially compatible with IEEE 802.3. Together, Ethernet and IEEE 802.3 currently maintain the greatest market share of any local-area network (LAN) protocol. Today, the term Ethernet is often used to refer to all carrier sense multiple access collision detect (CSMA/CD) LANs that generally conform to Ethernet specifications, including IEEE 802.3.
When it was developed, Ethernet was designed to fill the middle ground between long-distance, low-speed networks and specialized, computer-room networks carrying data at high speeds for very limited distances. Ethernet is well suited to applications on which a local communication medium must carry sporadic, occasionally heavy traffic at high peak data rates.
Ethernet and IEEE 802.3
Ethernet and IEEE 802.3 specify similar technologies. Both are CSMA/CD LANs. Stations on a CSMA/CD LAN can access the network at any time. Before sending data, CSMA/CD stations "listen" to the network to see if it is already in use. If it is, the station wanting to transmit waits. If the network is not in use, the station transmits. A collision occurs when two stations listen for network traffic, "hear" none, and transmit simultaneously. In this case, both transmissions are damaged, and the stations must retransmit at some later time. Back-off algorithms determine when the colliding stations retransmit. CSMA/CD stations can detect collisions, so they know when they must retransmit. This access method is used by traditional Ethernet and IEEE 802.3 functions in half-duplex mode. (When Ethernet is operated in full-duplex mode, CSMA/CD is not used.) This means that only one station can transmit at a time over the shared Ethernet.
This access method was conceived to offer shared and fair access to multiple network stations/devices. It allows these systems fair access to the Ethernet network through a process of arbitration by dictating how stations attached to this network can access the shared channel. It allows stations to listen before transmitting and can recover if signals collide. This recovery time interval is called a slot time and is based on the round-trip time that it takes to send a 64-byte frame the maximum length of an Ethernet LAN attached by repeaters. Another name for this shared LAN is a collision domain. For half-duplex operation, the mode on which traditional Ethernet is based, the size of your collision domain can be limited by the physical limitations of the cabling utilized. Table 4-1 lists the collision domains for 10/100/1000 Mbps.
The limitations of the cable itself can create even smaller boundaries.
Because the 64-byte slot time is consistent for 10/100/1000 transmission speeds, this severely limits the scalability for 1000BaseX to operate in a network with a diameter of more than 20 meters. To overcome this obstacle, use carrier extension bits in addition to the Ethernet frame size to extend the time that transmits on the wire. This expands the network diameter to 100 meters per segment, like 100BaseT.
For this system to work, everyone must abide by the same rules. For CSMA/CD the rules are as follows:
1. ![]() Listen—Stations listen for signals on the wire. If a signal is detected (carrier sense), then stations should not attempt to transmit frame. If a station "hears" another signal on the wire while transmitting the first 64 bytes of a frame, it should recognize that its frame has collided with another.
Listen—Stations listen for signals on the wire. If a signal is detected (carrier sense), then stations should not attempt to transmit frame. If a station "hears" another signal on the wire while transmitting the first 64 bytes of a frame, it should recognize that its frame has collided with another.
2. ![]() Collision detect—If a station detects a collision, it must back off from sending the frame using the truncated back-off algorithm. The back-off algorithm counts the number of collisions, if any, to determine how long a station must wait to retransmit the frame. This algorithm backs off each time that a collision is detected. The goal of this method is to provide the system a way to determine how many stations are trying to transmit simultaneously and then guess when it should be safe to try again. The way that the truncated back-off algorithm tracks and adjusts timers is based on the value of 2n , where n is the number of collisions encountered during transmission of the frame. The result is a guess of how many stations may be on the shared channel. This result gets plugged in as a range, counting from zero, for the number of slot times to wait. The algorithm randomly selects a value from this range as shown in Table 4-2.
Collision detect—If a station detects a collision, it must back off from sending the frame using the truncated back-off algorithm. The back-off algorithm counts the number of collisions, if any, to determine how long a station must wait to retransmit the frame. This algorithm backs off each time that a collision is detected. The goal of this method is to provide the system a way to determine how many stations are trying to transmit simultaneously and then guess when it should be safe to try again. The way that the truncated back-off algorithm tracks and adjusts timers is based on the value of 2n , where n is the number of collisions encountered during transmission of the frame. The result is a guess of how many stations may be on the shared channel. This result gets plugged in as a range, counting from zero, for the number of slot times to wait. The algorithm randomly selects a value from this range as shown in Table 4-2.
|
2n value1
|
Actions
|
|
20-1 |
Stations either try to retransmit immediately or wait for one slot time. |
|
22 |
Stations randomly wait zero, one, two, or three slot times to retransmit. |
|
23 |
Stations randomly wait from zero to seven slot times. |
|
24 |
. . . you get the point. |
|
1 2n where n = the number of collisions |
Depending on the number of collisions the algorithm randomly selects to back off, a station could potentially wait a while before retransmitting.
The algorithm collision counter stops incrementing at 10, where the penalty wait time is selected from a range of 0 to 1023 slot times before retransmission. This is pretty bad, but the algorithm will attempt to retransmit the frame up to 16 collisions. Then it just gives up, and a higher-layer network protocol such as TCP/IP will attempt to retransmit the packet. This is an indication that you have some serious errors.
When a station successfully sends a frame, the collision counter (penalty) is cleared (for that frame) and no loner must wait for the back-off time. ("Interface" statistics are not cleared, just the timer is). Any stations with the lowest collisions will be capable of accessing the wire more quickly because they do not have to wait.
Both Ethernet and IEEE 802.3 LANs are broadcast networks. In other words, all stations see all frames, regardless of whether they represent an intended destination. Each station must examine received frames to determine whether the station is a destination. If it is a destination, the frame is passed to a higher protocol layer for appropriate processing.
Differences between Ethernet and IEEE 802.3 standards are subtle. Ethernet provides services corresponding to Layers 1 and 2 of the OSI reference model, whereas IEEE 802.3 specifies the physical layer (Layer 1) and the channel-access portion of the link layer (Layer 2), but does not define a logical link control protocol. Both Ethernet and IEEE 802.3 are implemented in hardware. Typically, the physical manifestation of these protocols is either an interface card in a host computer or circuitry on a primary circuit board within a host computer.
Now, having said all that regarding the regular operation of traditional Ethernet and 802.3, we must discuss where the two separate in features and functionality. The IEEE 802.3 standard was based on traditional Ethernet, but improvements have been made to this current standard. What we have discussed so far will not scale in today's demanding service provider and enterprise networks.
Full-Duplex Operation 10/100/1000
Everything you've read so far dealt with half-duplex operation (CSMA/CD, back-off timers, and so on). Full-duplex mode allows stations to transmit and receive data simultaneously. This makes for more efficient use of the available bandwidth by allowing open access to the medium. Conversely, this mode of operation can function only with Ethernet switching hubs or via Ethernet cross-over cables between interfaces capable of full-duplex Ethernet. Full-duplex mode expects links to be point-to-point links. There are also no collisions in full-duplex mode, so CSMA/CD is not needed.
Autonegotiation
Autonegotiation allows Ethernet devices to automatically configure their interfaces for operation. If the network interfaces supported different speeds or different modes of operation, they will attempt to settle on a lower common denominator. A plain repeater cannot support multiple speeds; it knows only how to regenerate signals. Smart hubs employ multiple repeaters and a switch plane internally to allow stations that support different speeds to communicate. The negotiation is performed only when the system initially connects to the hub. If slower systems are attached to the same smart hub, then faster systems will have to be manually configured for 10 Mbps operation.
To make sure that your connection is operating properly, IEEE 802.3 Ethernet employs normal link pulses (NLPs), which are used for verifying link integrity in a 10BaseT system. This signaling gives you the link indication when you attach to the hub and is performed between two directly connected link interfaces (hub-to-station or station-to-station). NLPs are helpful in determining that a link has been established between devices, but they are not a good indicator that your cabling is free of problems.
An extension of NLPs is fast link pulses. These do not perform link tests, but instead are employed in the autonegotiation process to advertise a device's capabilities. Autonegotiation on 1000BaseX networks works at only 1000 Mbps, so the only feature "negotiated" is for full- or half-duplex operation. There may be new vendor implementations on the market that can autonegotiate speeds 10 to 1000BaseX, but at this time they are not widely deployed.
A backup alternative, called parallel detection, works for 10/100 speeds if autonegotiation is disabled or is unsupported. This is basically a fallback mechanism that springs into action when autonegotiation fails. The interface capable of autonegotiation will configure itself for bare bones 10-Mbps half-duplex operation.
Physical Connections
IEEE 802.3 specifies several different physical layers, whereas Ethernet defines only one. Each IEEE 802.3 physical layer protocol has a name that summarizes its characteristics. The coded components of an IEEE 802.3 physical layer name are shown in Figure 4-1.
Figure 4-1 IEEE 802.3 Physical Layer Name Components
A summary of Ethernet Version 2 and IEEE 802.3 characteristics appears in Tables 4-3 and 4-4.
There are other 100Basen implementations, but they are not widely implemented for various reasons. One particular case in point is 100BaseT4. This system uses four pairs of copper wire and can be used on voice- and data-grade cable. 10/100BaseT systems perform well on Category 5 data-grade cable and use only two pairs of copper wire.
Ethernet is most similar to IEEE 802.3 10Base5. Both of these protocols specify a bus topology network with a connecting cable between the end stations and the actual network medium. In the case of Ethernet, that cable is called a transceiver cable. The transceiver cable connects to a transceiver device attached to the physical network medium. The IEEE 802.3 configuration is much the same, except that the connecting cable is referred to as an attachment unit interface (AUI), and the transceiver is called a media attachment unit (MAU). In both cases, the connecting cable attaches to an interface board (or interface circuitry) within the end station.
Frame Formats
Ethernet and IEEE 802.3 frame formats are shown in Figure 4-2.
Figure 4-2 Ethernet and IEEE 802.3 Frame Formats
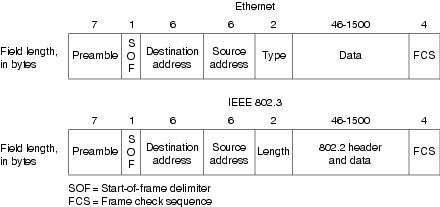
Both Ethernet and IEEE 802.3 frames begin with an alternating pattern of ones and zeros called a preamble. The preamble tells receiving stations that a frame is coming.
The byte before the destination address in both an Ethernet and an IEEE 802.3 frame is a start-of-frame (SOF) delimiter. This byte ends with 2 consecutive 1 bits, which serve to synchronize the frame reception portions of all stations on the LAN.
Immediately following the preamble in both Ethernet and IEEE 802.3 LANs are the destination and source address fields. Both Ethernet and IEEE 802.3 addresses are 6 bytes long. Addresses are contained in hardware on the Ethernet and IEEE 802.3 interface cards. The first 3 bytes of the addresses are specified by the IEEE on a vendor-dependent basis, and the last 3 bytes are specified by the Ethernet or IEEE 802.3 vendor. The source address is always a unicast (single node) address, whereas the destination address may be unicast, multicast (group), or broadcast (all nodes).
In Ethernet frames, the 2-byte field following the source address is a type field. This field specifies the upper-layer protocol to receive the data after Ethernet processing is complete.
In IEEE 802.3 frames, the 2-byte field following the source address is a length field, which indicates the number of bytes of data that follow this field and precede the frame check sequence (FCS) field.
Following the type/length field is the actual data contained in the frame. After physical layer and link layer processing is complete, this data will eventually be sent to an upper-layer protocol. In the case of Ethernet, the upper-layer protocol is identified in the type field. In the case of IEEE 802.3, the upper-layer protocol must be defined within the data portion of the frame, if at all. If data in the frame is insufficient to fill the frame to its minimum 64-byte size, padding bytes are inserted to ensure at least a 64-byte frame.
In 802.3 the data field carries a payload header in addition to the payload itself. This header serves the logical link control sublayer of the OSI model and is completely independent of the MAC sublayer and physical layer below it. This header, functionally known as 802.2 encapsulation, contains destination service access point (DSAP) and source service access point (SSAP) information. This will notify higher protocols what type of payload is actually riding in the frame. It functions like the "type" field in traditional Ethernet and is used by upper-layer network protocols such as IPX. Network software developed to support the TCP/IP networking suite uses the type field to determine protocol type in an Ethernet frame. The type field and the LLC header are not replacements for each other, but they serve to offer backward compatibility between network protocol implementations without rewriting the entire Ethernet frame.
After the data field is a 4-byte frame check sequence (FCS) field containing a cyclic redundancy check (CRC) value. The CRC is created by the sending device and is recalculated by the receiving device to check for damage that might have occurred to the frame in transit.
Troubleshooting Ethernet
Table 4-5 provides troubleshooting procedures for common Ethernet media problems.
When you're troubleshooting Ethernet media in a Cisco router environment, the show interfaces ethernet command provides several key fields of information that can assist with isolating problems. The following section provides a detailed description of the show interfaces ethernet command and the information that it provides.
show interfaces ethernet
Use the show interfaces ethernet privileged exec command to display information about an Ethernet interface on the router:
•![]() show interfaces ethernet unit [accounting]
show interfaces ethernet unit [accounting]
•![]() show interfaces ethernet [slot | port] [accounting] (for the Cisco 7200 series and Cisco 7500)
show interfaces ethernet [slot | port] [accounting] (for the Cisco 7200 series and Cisco 7500)
•![]() show interfaces ethernet [type slot | port-adapter | port] (for ports on VIP cards in the Cisco 7500 series routers)
show interfaces ethernet [type slot | port-adapter | port] (for ports on VIP cards in the Cisco 7500 series routers)
Syntax Description
unit—This must match a port number on the selected interface.
accounting—(Optional) This displays the number of packets of each protocol type that have been sent through the interface.
slot—Refer to the appropriate hardware manual for slot and port information.
port—Refer to the appropriate hardware manual for slot and port information.
port-adapter—Refer to the appropriate hardware manual for information about port adapter compatibility.
Command Mode
Privileged exec
Usage Guidelines
This command first appeared in Cisco IOS Release 10.0. If you do not provide values for the argument unit (or slot and port on the Cisco 7200 series, or slot and port-adapter on the Cisco 7500 series), the command will display statistics for all network interfaces. The optional keyword accounting displays the number of packets of each protocol type that have been sent through the interface.
Sample Display
The following is sample output from the show interfaces command for the Ethernet 0 interface:
Router# show interfaces ethernet 0
Ethernet 0 is up, line protocol is up
Hardware is MCI Ethernet, address is aa00.0400.0134 (via 0000.0c00.4369)
Internet address is 131.108.1.1, subnet mask is 255.255.255.0
MTU 1500 bytes, BW 10000 Kbit, DLY 1000 usec, rely 255/255, load 1/255
Encapsulation ARPA, loopback not set, keepalive set (10 sec)
ARP type: ARPA, PROBE, ARP Timeout 4:00:00
Last input 0:00:00, output 0:00:00, output hang never
Output queue 0/40, 0 drops; input queue 0/75, 2 drops
Five minute input rate 61000 bits/sec, 4 packets/sec
Five minute output rate 1000 bits/sec, 2 packets/sec
2295197 packets input, 305539992 bytes, 0 no buffer
Received 1925500 broadcasts, 0 runts, 0 giants
3 input errors, 3 CRC, 0 frame, 0 overrun, 0 ignored, 0 abort
0 input packets with dribble condition detected
3594664 packets output, 436549843 bytes, 0 underruns
8 output errors, 1790 collisions, 10 interface resets, 0 restarts
Table 4-6 presents show interfaces ethernet field descriptions.
